They are really a person-way capabilities – Meaning that it is unfeasible to use the hash value to figure out what the initial input was (with present technology and tactics).To authenticate customers during the login approach, the procedure hashes their password inputs and compares them for the saved MD5 values. Should they match, the consumer g
 Jaleel White Then & Now!
Jaleel White Then & Now! Daniel Stern Then & Now!
Daniel Stern Then & Now!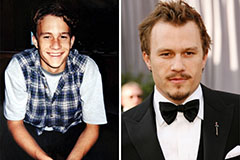 Heath Ledger Then & Now!
Heath Ledger Then & Now! Rossy de Palma Then & Now!
Rossy de Palma Then & Now! Ricky Schroder Then & Now!
Ricky Schroder Then & Now!